Sitecore recently updated their docker images to use ltsc2022. Martin Miles showed us what that means for developers and how to update your container environment to run Sitecore in process isolation mode. In short, process isolation is again a viable option to improve performance of running containers locally. I was hopeful the ltsc2022 images were tied to the update version 22H2 meaning they would work on Windows 10 22H2. But alas, they only work on Windows 11 22H2 and above. We are still using windows 10 within Perficient, so I setup a virtual machine to test out windows 11 and the new ltsc2022 images. It wasn’t as easy as I thought it would be.
Creating a Windows 11 VM
I started from a VM with Windows 10 to perform an upgrade using the Windows 11 disk image (.iso) file. Afterward, I quickly discovered that my VM did not meet the requirements for Windows 11.
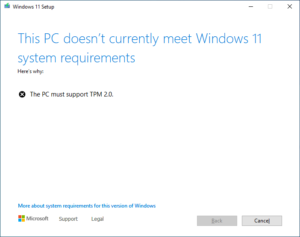
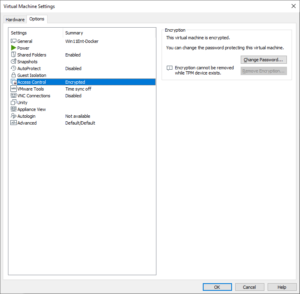
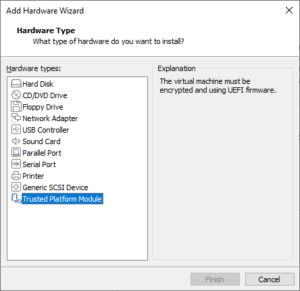
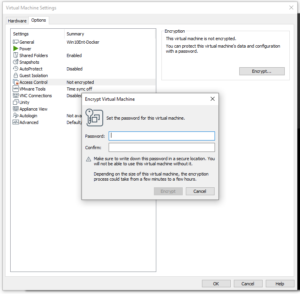
I need to install the Trusted Platform Module (TPM). In order to add that module to the VM, I had to first encrypt the VM.
With these two requirements met, the upgrade process proceeded smoothly and I had a VM running Windows 11.
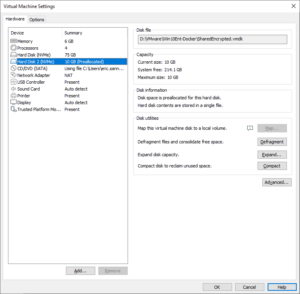
Using a shared virtual drive
In a previous post, I detailed how I created a shared drive for docker data. Unfortunately, that won’t work on the Windows 11 VM. Windows 11 wants the drive to be encrypted.
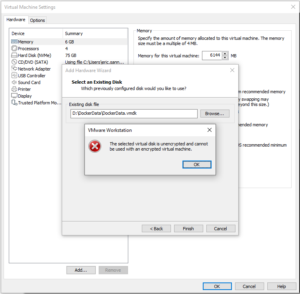
You can’t encrypt a vhd directly. You have to attach it to an unencrypted VM and encrypt the VM. Even if both VMs are encrypted, you can’t add an encrypted drive that is attached to another VM.
![]() Adding a drive
Adding a drive
While you can’t use a shared drive, you can add addition drives to the encrypted VM. The normal process works as expected. You can also use the other disk utilities to expand and compact an encrypted drive.
Removing a drive
You cannot remove a drive while the VM is encrypted. The button to remove the drive is disabled.
The virtual machine config file (.vmx) is also encrypted so you cannot modify it manually. You cannot unencrypt the drive while TPM is added to the VM.
VMWare gives you a warning “removing the TPM module will render the encrypted data unrecoverable”. But you can remove the TPM and still unencrypt the VM. Then you can remove your additional drives. Then add back the TPM and encrypt the VM again. This is all very time consuming based on the size of the drive. It took about 15 minutes to decrypt and 15 minutes to encrypt a VM with a 100GB vhd. Not very effective if you want to share a drive with multiple VMS to decrypt and encrypt every time you use a different VM.
On the other hand
It turns out the Windows 11 VM will run in an unencrypted state with TPM removed. You can even get Windows updates. It just has to be there to create a new VM or upgrade a VM from a previous version of Windows. Then you can add, share, and remove drives.
Process Isolation
We still see a massive performance improvement just running nanoserver in process isolation mode.
| Process | Hyperv | |
| CPU | 0.0 % | 0.19% |
| Memory | 26.7MB | 236MB |
You can test on your local with the following commands:
- docker run -it –name ns22h –isolation hyperv mcr.microsoft.com/windows/nanoserver:ltsc2022 cmd.exe
- docker run -it –name ns22p –isolation process mcr.microsoft.com/windows/nanoserver:ltsc2022 cmd.exe
Final Thoughts
Keep in mind the ltsc2022 images will only run in process isolation mode on Windows 11 version 22H2. Once we get to 23H1, you will have to run the containers in hyperv mode again. As I mentioned in a previous post about isolation modes, you can avoid windows updates for some time and stay on 22H2. But at some point, windows will force you to update to a newer version at which point we’ll have to wait for new container images to be created and adopted.