Whether your company has 10 people or 10,000 people, security measures need to be in place to ensure a safe, secure, and compliant environment for your end users. Many companies will often be required to adhere to certain security regulations and compliance standards but rest assured Microsoft has your back. Microsoft understands this need for security so they have built their security around Office 365 hyper-scale, enterprise-grade cloud to ensure your organization remains compliant. In today’s article we’ll do a high level overview of what Teams has to offer its customers in terms of security and compliance. This blog will be geared more towards those of you making the executive decisions rather than a technical deep dive (but I’ll be doing this in a subsequent blog, so stay tuned). Without further ado, let’s talk compliance!
At a high level, security and compliance in Microsoft Teams is composed of the following topics:
- Auditing & reporting
- Content search
- Conditional access
- eDiscovery
- Identity models & authentication
- Information barriers
- Legal hold
- Licensing
- Location of data
- Retention policies
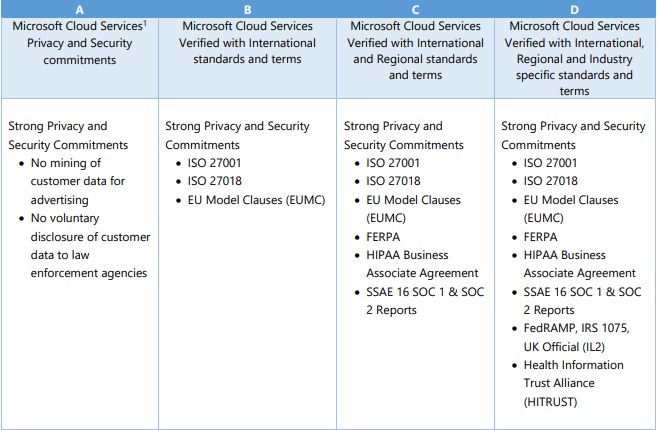
Although this list may seem daunting, Microsoft has done a great job of explaining each of these topics in depth so you can ensure your company is up to snuff on your security and compliance. Microsoft Teams has also recently (apparently SO recently that they haven’t updated their compliance framework table) become Tier-D compliant. If you are unfamiliar with how this is categorized, basically Microsoft has something called the Microsoft compliance framework and they categorize their Office 365 applications and services into 4 categories (A, B, C, or D). Each of these categories is defined based upon specific commitments that must be met by that particular Office 365 application/service. Industry leading compliance commitments will fall into either tier C or D and are enabled by default. However, services in tiers A or B will come with the ability to enable/disable these services for the entire organization and will be controlled by an admin. For a deeper dive on the Microsoft compliance framework you can checkout the link here.
So now that we know what specifications need to be met to ensure compliance, let’s go over each of the bullets above so you can get a deeper understanding of what Teams has to offer!
Auditing & Reporting in Teams
Do you need to find if someone has been peeping at documents they shouldn’t be or maybe they tried to delete something from their mailbox that they don’t want anyone else seeing. Fear not, audit logs have come to the rescue! Using the Office 365 Security and Compliance Center you can use audit logs to find and administer activity in your organization. This capability is not limited to Teams, you can actually search user and admin activity in Office 365 for cases like:
- User activity in SharePoint Online and OneDrive for Business
- User activity in Exchange Online (Exchange mailbox audit logging)
- Admin activity in SharePoint Online
- Admin activity in Azure Active Directory (the directory service for Office 365)
- Admin activity in Exchange Online (Exchange admin audit logging)
- User and admin activity in Sway
- eDiscovery activities in the security and compliance center
- User and admin activity in Power BI
- User and admin activity in Microsoft Teams
- User and admin activity in Dynamics 365
- User and admin activity in Yammer
- User and admin activity in Microsoft Flow
- User and admin activity in Microsoft Stream
- Analyst and admin activity in Microsoft Workplace Analytics
- User and admin activity in Microsoft PowerApps
Content Search
Within the compliance center of Office 365 you can use the Content Search eDiscovery tool to search for emails, documents, and IM conversations in your organization. Just like with audit logs this tool can be used across multiple Office 365 services:
- Exchange Online mailboxes and public folders
- Sharepoint Online sites and OneDrive for Business accounts
- Skype for Business conversations
- Microsoft Teams
- Office 365 Groups
Once a search has been conducted you can view statistics about the search results. This will include a summary of the search results, query statistics, and the name of content locations that have the most matching items.
Conditional Access
The name speaks for itself! Conditional Access allows you to access certain services under certain conditions. As you see in the diagram below conditional access is composed of conditions and controls.
So based on a condition above (application, device status, locations, sign in risk, or user attribute) a control will take place meaning “do this” (i.e. Allow access or Block access).
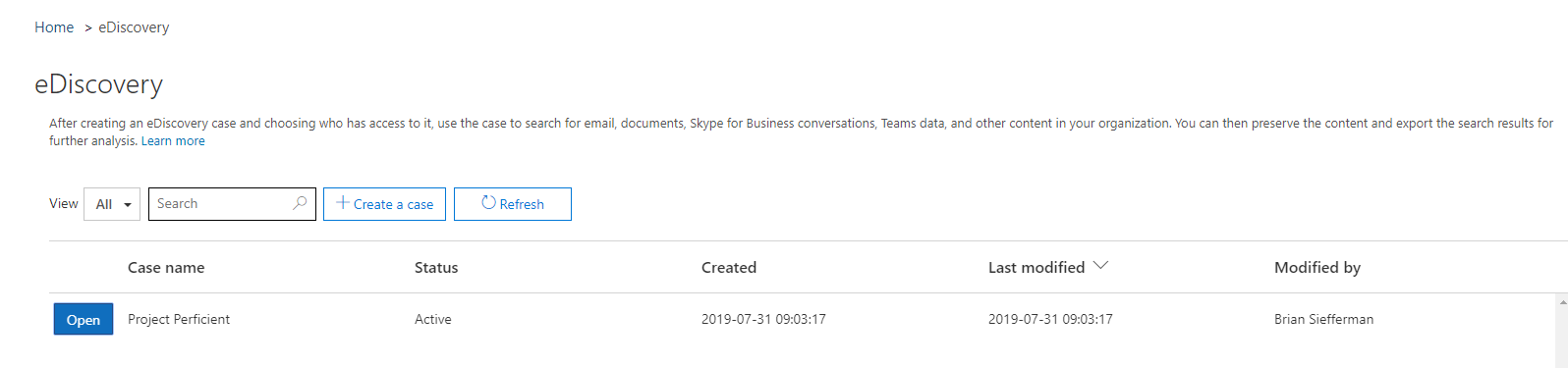
eDiscovery
According to Microsoft, “electronic discovery is the electronic aspect of identifying, collecting and producing electronically stored information (ESI) in response to a request for production in a law suit or investigation.” Often times, an enterprise will need to provide this ESI in order to avoid harsh legal penalties. Fear not, with the Security and Compliance Center in Office 365 you’ll have the ability to find this data within not only Microsoft Teams but also Exchange Online, SharePoint Online, Office 365 Groups, and OneDrive for Business. In addition, you’ll have the ability to conduct both in-place eDiscovery & Advanced eDiscovery (depending on licensing).
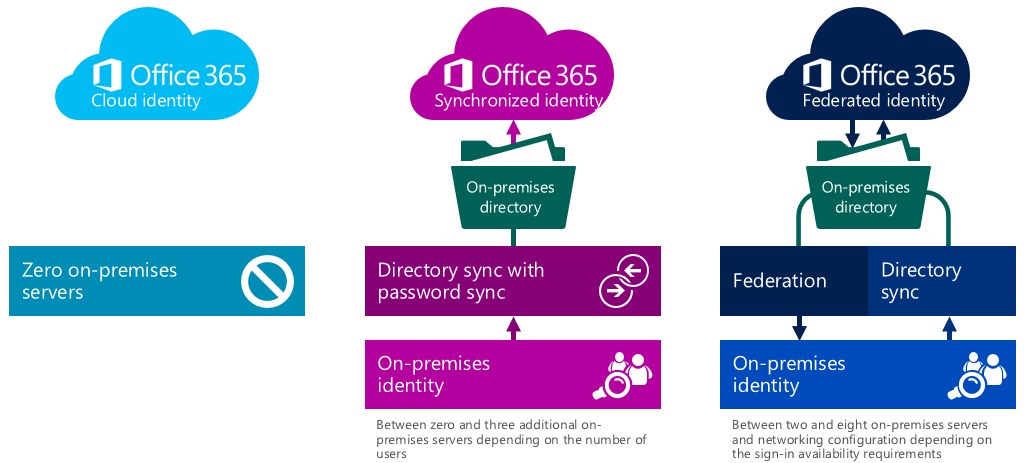
Identity Models and Authentication
Microsoft has gone through great lengths to ensure compatibility between Microsoft Teams and other products in the Office 365 suite. The identity models available in Office 365 are no exception. Microsoft Teams supports all 3 identity models:
- Cloud Identity – Users are created and managed in Office 365 and stored in Azure AD along with passwords being verified within Azure AD.
- Synchronized Identity – User identity is managed on-premises and the account and password hashes are synced to the cloud.
- Federated Identity – User identity is authenticated against the on-premises AD environment via ADFS or third-party identity provider. This will require a synchronized identity with the user password to be verified by the on-premises identity but the password hash won’t need to synchronized to Azure AD.
In addition, Microsoft Teams gives you the ability to leverage MFA (Multi-Factor Authentication) which will increase your user login security for all Office 365 services. MFA in Teams is supported by both tenant types:
- Cloud Only
- Phone Call
- Text Message
- Mobile App Notification
- Mobile App Verification Code
- Hybrid (Synchronized or Federated Identities)
- MFA for Office 365
- Azure MFA module (ADFS integrated)
- Physical or virtual smart card (ADFS integrated)
Information Barriers
Need to regulate how people within your organization communicate with one another? I introduce to you, Information barriers! Information barriers are policies that your admin can configure to prevent a certain individual or an entire group from communicating with each other. If you have information that should only be seen by the eyes of one particular group, you can use information barrier policies to ensure this information never gets beyond that group. Information barriers can be useful in the following scenarios:
- You need to prevent a team from communicating/sharing data with another specific team
- You need to prevent a team from communicating/sharing data with ANYONE outside of the team
Legal Hold
Legal hold is often a necessity when litigation is afoot. Legal hold allows you preserve all data associated with a user or team so that you can use this as evidence in a legal case. This is achieved by placing the user’s mailbox or a team on legal hold. In addition there are two ways to put a team on hold:
- In-Place Hold – putting a subset of a user’s entire mailbox/site collection on hold for the purpose of retaining only certain types of email
- Litigation Hold – putting a user’s entire mailbox/site collection on hold for the purpose of retaining it for legal review
Regardless of the method chosen above, the hold will always be placed on the groups mailbox. This way if the end user tried to cover their tracks by deleting/editing the channel messages that have been ingested into the mailbox, you will still have the unaltered copies of the content available to you within eDiscovery search.
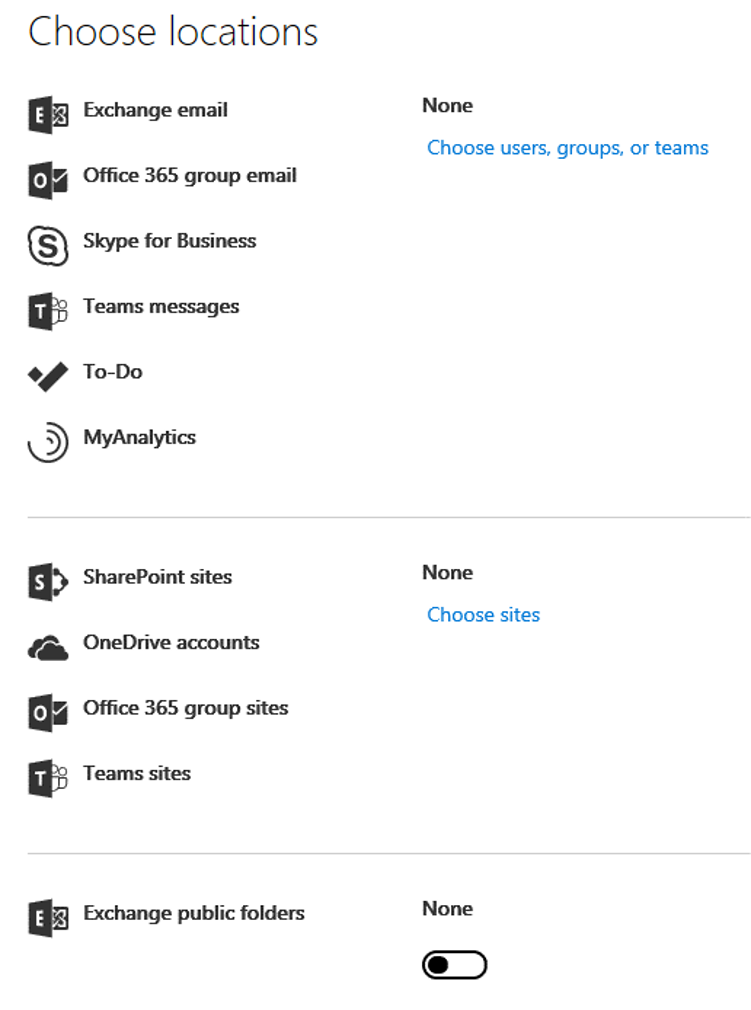
Licensing
If you’re like me, licensing in Office 365 can be quite daunting with all the different license types offered. Luckily Microsoft makes this pretty clear cut when it comes to security and compliance. Please refer to the table below which is provided by Microsoft to determine which licenses you believe should be applied to your end users. As you may notice, E3 and E5 licenses will give you the best bang for your buck when it comes to fulfilling the information protection capabilities.
| Information Protection Capability | Office 365 Business Essentials | Office 365 Business Premium | Office 365 Enterprise E1 | Office 365 Enterprise E3/E4 | Office 365 Enterprise E5 |
|---|---|---|---|---|---|
| Archive | – | – | – | Yes | Yes |
| In-Place eDiscovery | – | – | – | Yes | Yes |
| Advanced eDiscovery | – | – | – | – | Yes |
| Legal Hold | – | – | – | Yes | Yes |
| Compliance Content Search | – | Yes | Yes | Yes | Yes |
| Auditing and Reporting | Yes | Yes | Yes | Yes | Yes |
| Conditional Access* | Yes | Yes | Yes | Yes | Yes |
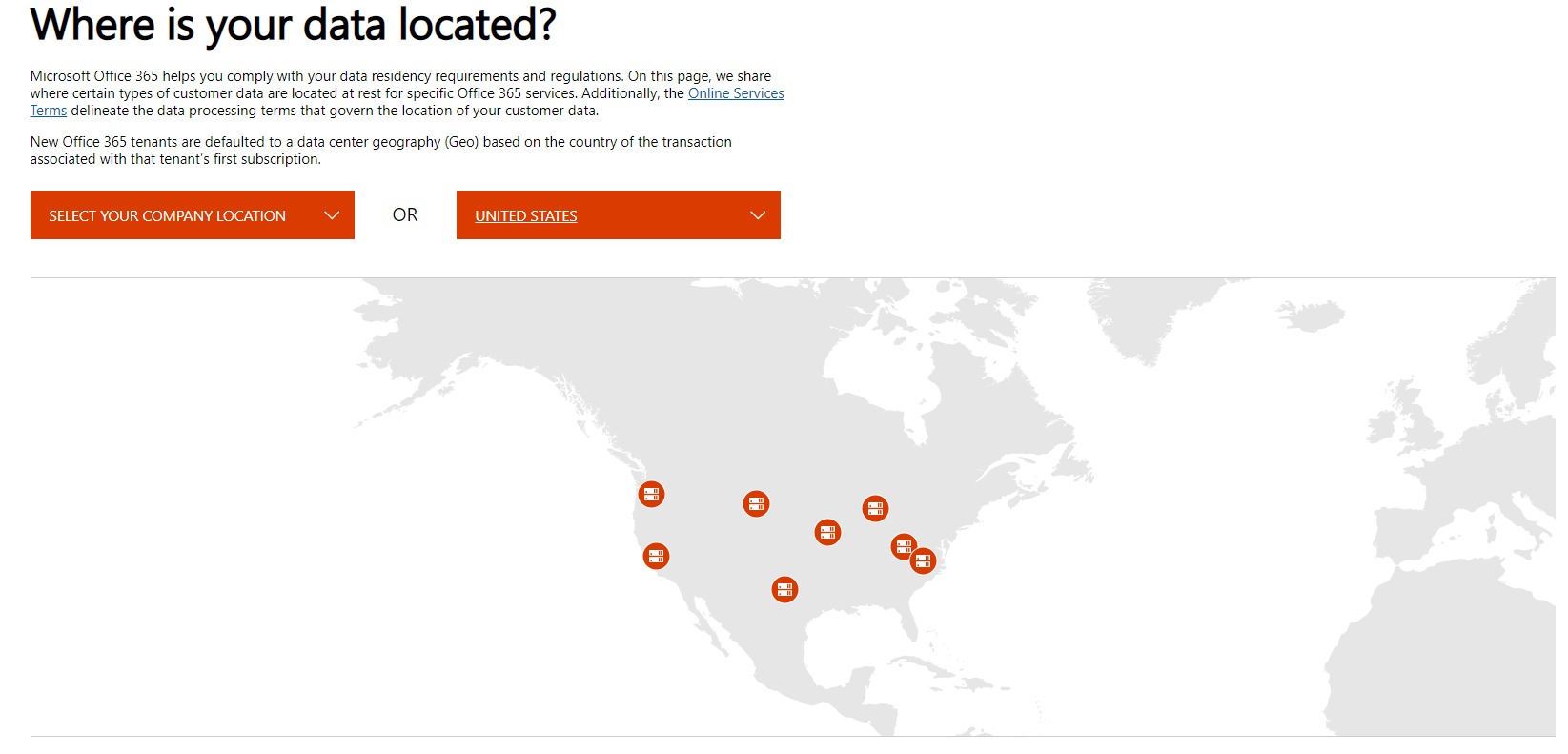
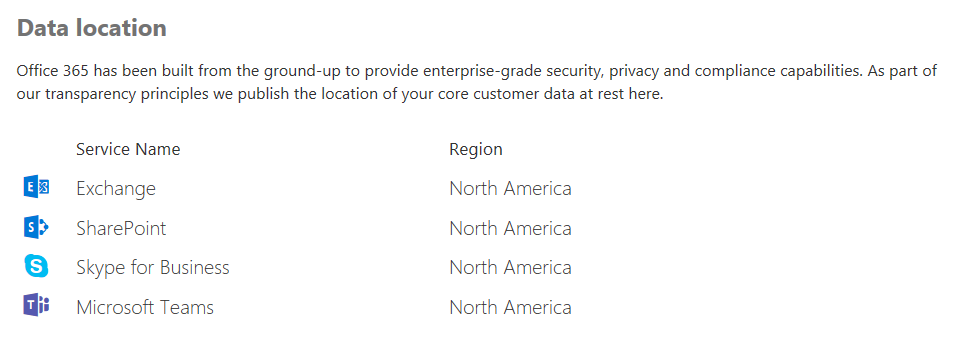
Location of Data in Teams
To put it simply, your Teams data resides in the region associated with your Office 365 tenant. Teams is currently supported in the following regions:
- Australia
- Canada
- France
- India
- Japan
- UK
- Americas
- APAC
- EMEA
If you’re still unsure where you data resides you can always check within your tenant by going to: Microsoft 365 admin center > Settings > Organization profile. Scroll down to Data location.
There you will see what region your Office 365 services reside in.
In addition, Microsoft has a nifty little URL where you can see Microsoft’s data center locations. For example, if your company is located within the United States like mine, you will see all of the data center locations within the US that service Microsoft Teams and all other Office 365 products:
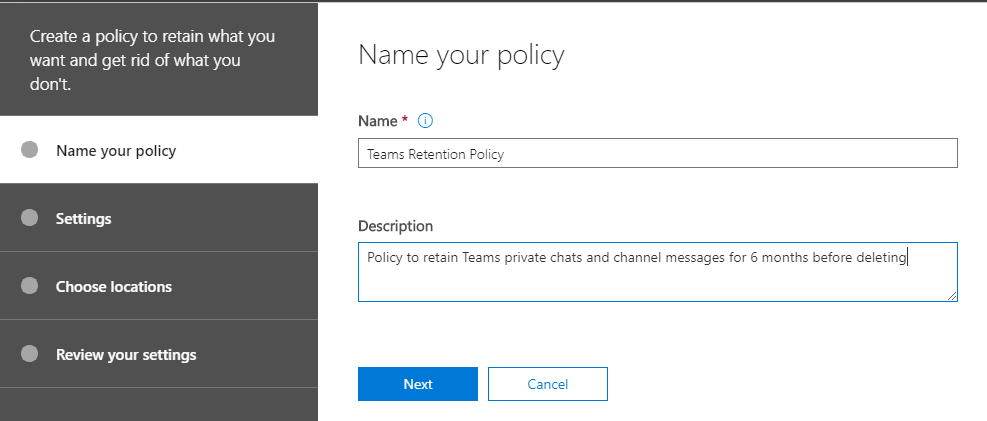
Retention Policies
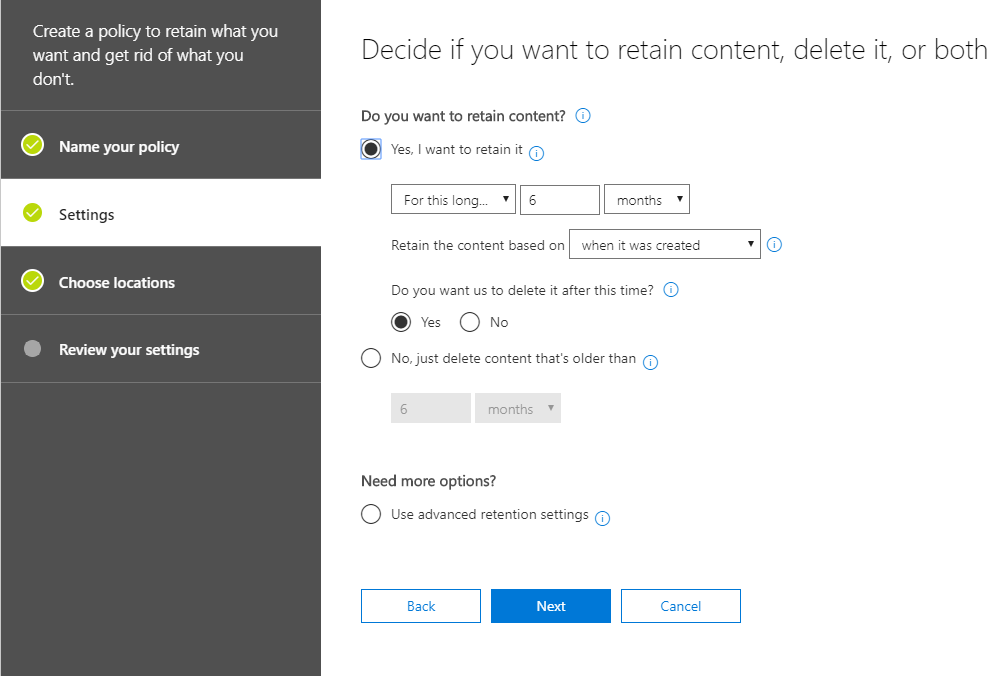
Last but certainly not least, we have retention policies. Retention might as well be Teams middle name since all Teams conversations are persistent and retained FOREVER by default. This is great in that it allows organizations to retain data (via preservation policy) for compliance purposes. However, some organization may not want this, as there are also certain liability issues that can arise if data is retained for too long, thus they need to make sure the data is deleted (via deletion policy). Luckily, this is where retention policies come in handy. With retention policies, admins will have the ability to create policies to either preserve or delete Teams chat and channel messages. This will allow you to cater to both scenarios while still remaining compliant. Currently Teams retention policies support the following scenarios:
- Do you want to retain content?
- Yes, I want to retain it – Content you choose stays where it currently lives. If users modify or delete the content, Microsoft will keep a copy of it in a secure location so you can get to it if you need to
- For this long…. (Days/Months/Years)
- Do you want us to delete it after this time?
- If yes, after this time Microsoft will delete the content from where it currently lives and the secure location where copies are stored. You’ll have a short time to recover the content before it is gone for good
- If no, content will be left in place. You’ll need to manually delete if you want it gone
- No, just delete content that’s older than
- (Days/Months/Years)
- Copies of content won’t be kept anywhere, so users will be free to permanently delete their email, docs, etc. But when content reaches the age you specify, Microsoft will automatically delete it where it lives at that time. That means emails, calendar items, Teams conversations, etc. will be deleted from users’ or group mailboxes and documents will be deleted from their SharePoint and OneDrive for Business libraries.
- (Days/Months/Years)
- Yes, I want to retain it – Content you choose stays where it currently lives. If users modify or delete the content, Microsoft will keep a copy of it in a secure location so you can get to it if you need to
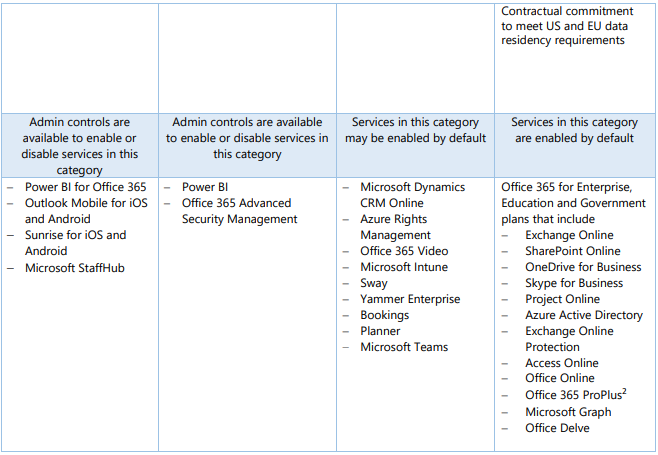
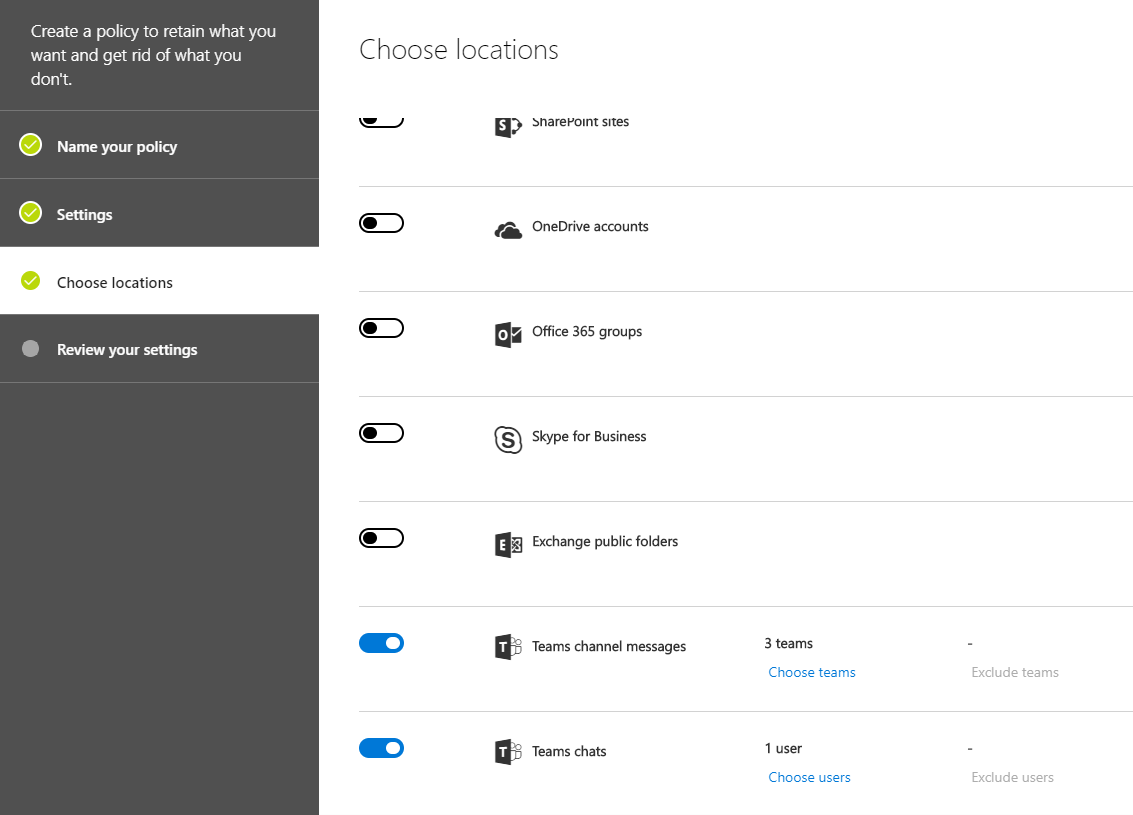
Lastly within the Security and Compliance Center you have the ability to set up separate retention policies for both Teams private chats (1:1 or 1:Many chats) and Teams channel messages. In the example below, I have created a policy called “Teams Retention Policy” where I will be retaining all Teams private chats and channel messages from the last 6 months before opting to delete the data.
After I have defined my policy I will configure the settings for my policy to reflect what I mentioned above.
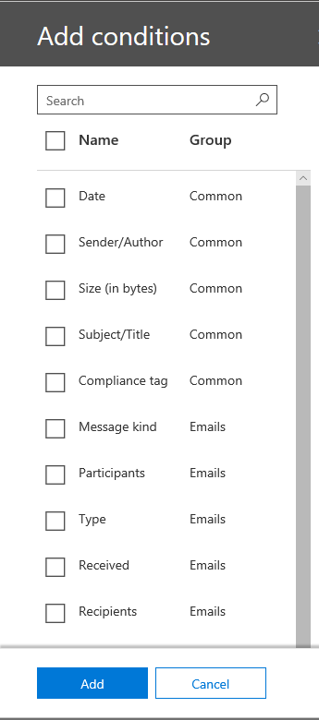
Then I configure the locations where I want the policy to be applied. In this instance I’ll also specify which teams and users I want to apply this policy to.
Finally you’ll just review what you have configured and save the retention policy! Piece of cake, right!?
This concludes the high level overview of the different security and compliance options you have within Microsoft Teams. Microsoft has big plans for Teams and they are constantly updating this service with the latest and greatest features and functionality. I encourage you to check back on a regular basis as I plan on doing a deep dive of most of these security and compliance features mentioned today. Nevertheless, I hope you have found this blog article helpful and I look forward to seeing you all in the next blog!