Meeting Payment Card Industry Data Security Standard (PCI DSS) compliance can be very complex and costly. If you are not clear how to achieve PCI compliance in a hybrid cloud environment, this article will guide you through the key points and considerations to get you there.
Firstly, there are various architectural options to choose from:
- Store sensitive data on a third-party provider’s infrastructure which is PCI DSS compliant.
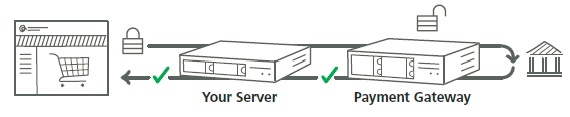
- Use a payment gateway’s encryption service to store and encrypt sensitive information. Your server can send this information via APIs to transmit sensitive information.
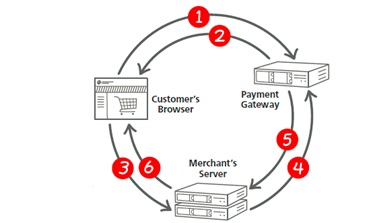
- Use a payment gateway’s encryption service to store and encrypt sensitive and transmit it to third-party via browser.
Upon getting the architectural guidelines, the following steps will help you get your infrastructure, either on private, public, or hybrid cloud, to PCI compliance.
- Understand PCI guidelines for cloud computing
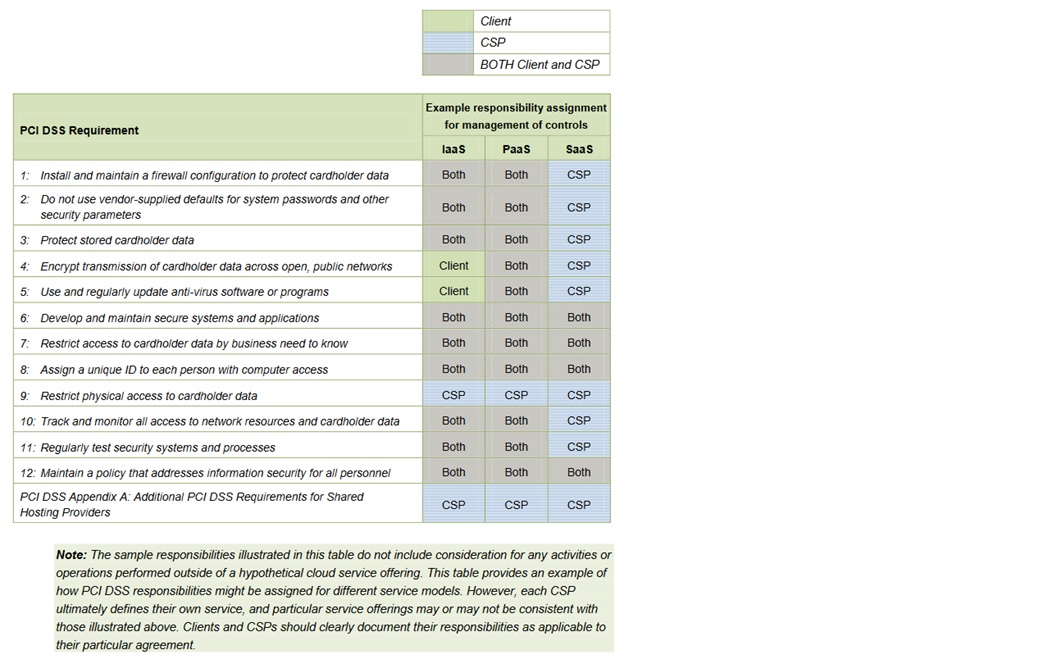
PCI has setup standards and guidelines for different deployment models such as public cloud, private cloud, community cloud, or hybrid cloud and for different cloud service categories. As per the guidelines, customer and cloud service provider secure their respective infrastructure. Exact responsibilities between customer and provider can be discovered at the early stages. Here is a sample of how PCI DSS responsibilities may be shared between clients and cloud service providers (CSP):
- Know your cloud provider
PCI guidelines give you set of questions for your cloud service provider to validate its PCI compliance. This information should be given to an auditor so that it can be verified during the audit process. Primarily, it’s your responsibility to meet the PCI compliance, so proof of compliance and certification must be checked. Ask questions of the CSP and verify the responses, for example:
- What does each service consist of exactly, and how is the service delivered?
- What does the service provide with respect to security maintenance, PCI DSS compliance, segmentation, and assurance? What is the client responsible for?
- How will the CSP provide ongoing evidence that security controls continue to be in place and are kept up to date?
- What will the CSP commit to in writing?
- Are other parties involved in the service delivery, security, or support?
- Think about security of complete infrastructure and understand significance of the PCI DSS compliance while deciding private vs public cloud
Remember that only servers that store sensitive information fall under this regulation, so you can choose private cloud only for PCI workload and other load can stay on public cloud; this option may provide some cost savings. Although PCI compliance is very important, it’s just a single component of overall security. It’s very important to start with the bigger picture and come down to the PCI compliance component of security so that you meet your comprehensive security needs.
- Get cloud-based compliance tools and automate compliance process as much as possible
Scalability, obviously, is an important part of being on cloud, so tools being used on traditional datacenters are not enough. Cloud-specific tools can provide security access across environments. To reduce the impact on operations and gain the full benefits of the cloud environment, security groups must get consistent visibility. Since operations of cloud environments are very agile, manual dependencies create bottlenecks. Compliance tools should be automated by integrating with tools such as Puppet and Chef.
- Create a long-term security approach for PCI implementation
Even if you plan to store PCI data on premise and to store other data on cloud, security should take care of both environments. Your solution should provide single view of overall security across cloud and on premise. The solution should have flexibility for future enhancements to meet long term vision.
In addition to the business and risk considerations, the implementation of security controls in a cloud environment may require specialized technical knowledge and skills. It is therefore crucial that, prior to migrating payment card operations into a cloud environment, an organization engages their technical, legal, due diligence, information security, and compliance teams to work together to define the client’s needs and evaluate potential cloud service offerings against those needs.
References:
www.pcisecuritystandards.org
www.cloudpassage.com
www.rackspace.com

Useful pointers on how to go about achieving PCI DSS compliance..