First let’s start off with what a Reverse proxy is and then cover how it fits in with with Skype for Business Server.
The Reverse proxy is a device that receives requests from clients on and then forwards the request on to another resource, in this case a Skype for Business Front End server. This is done in such a seamless manner that the Reverse Proxy is transparent to the client. Ideally, the Reverse Proxy device/appliance is placed between your internal Skype for Business Front End server/s and the public internet – the recommended placement would be in a DMZ network.
So why does Skype for Business (Skype4B) need a Reverse Proxy?
Skype4B relies on the Reverse Proxy to publish its Web Services to the public Internet.
Here are some of the Skype4B Web Service functions:
- Skype for Business Mobility client
- Simple URL’s
- LyncDiscover – client sign-in and discovery
- Meet – Connect to meetings
- Dialin – Dial-In Conference settings information
- Schedule – Schedule Meetings
- Skype for Business Web App client
- Expand Distribution Groups
- Address Book download
Let’s take a quick look at the IIS settings of a Front End Server in my lab; you will see that there are two different IIS sites (Image below). One web site for Internal and one for External.

Why are there separate Web Sites for Internal and External Web Services?
Not all Skype4B Web Services are designed to be exposed to the internet – examples would be the Skype4B Control Panel and the Response Group Configuration page. Skype for Business differentiates these sites by using different ports:
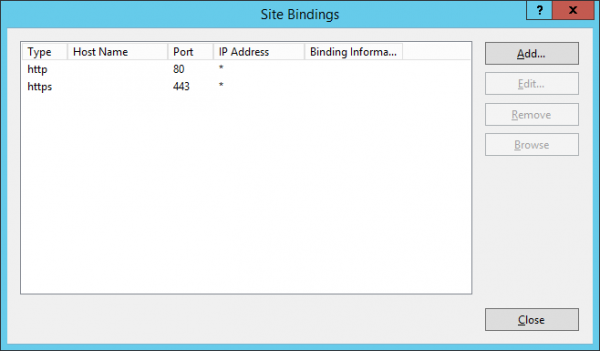
- Internal Web Site: 80 and 443
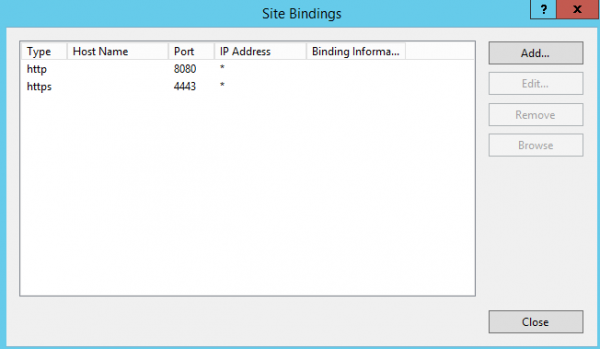
- External Web Site: 8080 and 4443
Using differencing ports also allows the Skype4B Front Ends to use a single IP address.
You can view the port bindings by selecting the site and ‘Edit Bindings’
- Skype for Business Server External Web Site – which is bound to port 8080 and 4443
- Skype for Business Server Internal Web Site – which is bound to port 443 and 80

Now that we know the purpose of the two web sites, this is really where the Reverse Proxy comes into play. The reverse proxy receives internet traffic on port 80 and 443 and then forwards that traffic to the Skype4B Front End/s on port 4443 and 8080. The blow graphic depicts the port change and the placement of the Reverse Proxy Device.
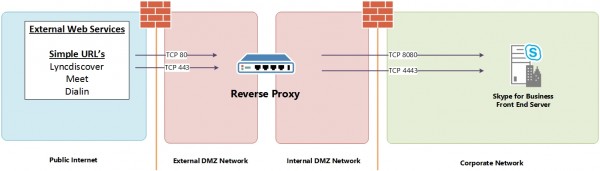
This allows the Skye4B Front Ends to remain on the LAN while the Reverse proxy is placed in your DMZ and exposed to the internet.
The Reverse Proxy is highly recommended for publishing External Web Services for a Skype4B deployment, but it is important to note that it is not a native Skype4B server role and another product/appliance must be used to provide this function.
To view the Reverse Proxy in action or even just testing the traffic is getting where it is supposed to be, you can run a packet capturing program on one of your Front End servers and see the 8080 and 4443 port traffic. (Wireshark image below)

Qualified Reverse proxies
This section lists the Skype4B qualified reverse proxy products that have completed solution testing with Skype4B Server. While any reverse proxy is expected to work with Skype4B Server, the reverse proxies listed below have completed extensive testing and are posted with detailed deployment white papers to assist in configuration.
Qualified for Lync Server 2013/Skype for Business Server 2015
| Mailbox Location | Lync/Skype account location | Preparation Required |
|---|---|---|
| Online | Online | Yes |
| On-premises | Online | Yes |
| Online | On-premises | Yes |
| On-premises | On-premises | No* |
** In November, 2012, Microsoft ceased license sales of Forefront Threat Management Gateway 2010, or TMG. TMG is still a fully supported product, and is still available for sale on appliances sold by third parties.
There are other solutions that can used as a successful solution while not being qualified; Apache and PFsense are a couple examples.


You have a typo in this line:
Skype for Business Server External Web Site – which is bound to port 8080 and 443
I think you mean 4443.
Good catch Jason! I will update the article
Greate article!
One proxy worth mentioning is Bastion that is part of a security suite for skype for business offering built in TFA , device registration, DDoS protection and more
Working on certifying soon…